A fake Ledger Live app appeared in Apple’s App Store and drained $9.5 million in cryptocurrency from more than 50 victims over just one week.
- A malicious Ledger Live clone on the Apple App Store steals $9.5 million from fifty victims through fraudulent seed phrase prompts.
- The exploit drained $3.23 million in USDT on April 9 and moved 5.92 BTC belonging to Garrett Dutton into KuCoin.
- This security failure contradicts Apple claims regarding App Store safety while funds circulate through more than 150 KuCoin deposit addresses.
Blockchain investigator ZachXBT flagged the malicious clone on Telegram. Victims downloaded the counterfeit app and entered their seed phrases after it displayed fake error messages that copied the real Ledger interface.
Apple removed the fake Ledger Live app Monday.
Stolen funds passed through more than 150 KuCoin deposit addresses tied to AudiA6, a centralized mixing service. ZachXBT shared theft addresses across Bitcoin, EVM chains, Tron, Solana and Ripple.
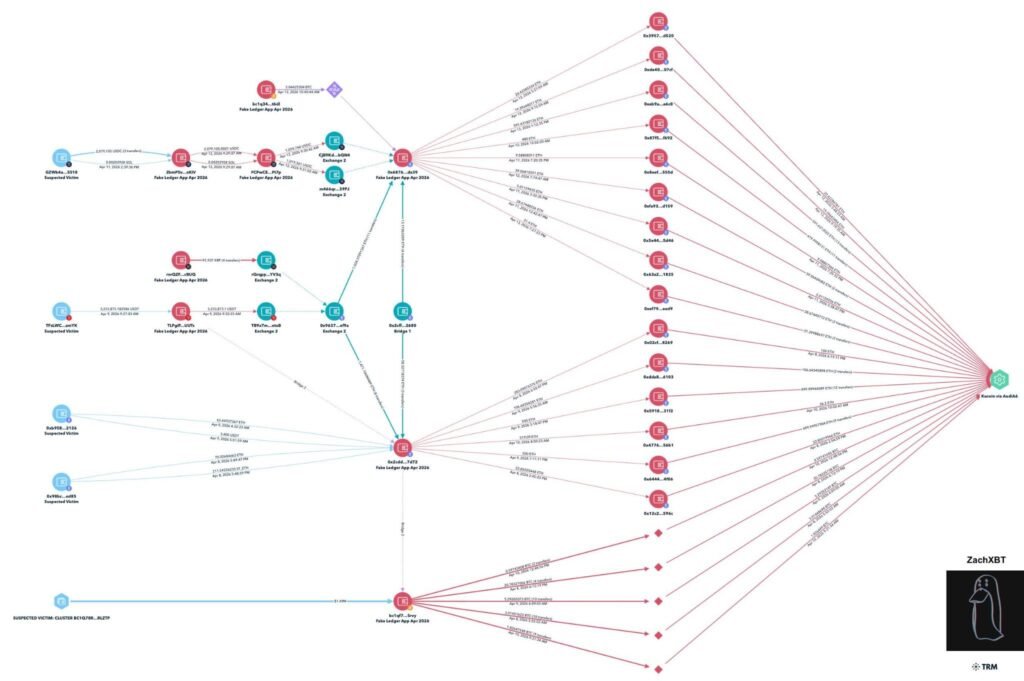
Three large losses stand documented. One victim lost $3.23 million in USDT on April 9. Another lost $2.079 million in USDC on April 11. A third lost roughly $1.95 million on April 8, including 20.64 BTC plus stETH and ETH.
Genuine News Deserves Honest Attention.
High-conviction projects require an intelligent audience. Connect with readers who value sharp reporting.
👉 Submit Your PRMusician Garrett Dutton, known as G. Love, lost 5.92 BTC worth about $424,000. He posted on X that he lost “my retirement fund in a hack/scam… All my BTC gone in an instant” after downloading the counterfeit app on a new MacBook and entering his 24-word seed phrase when the software prompted him with a critical error. The funds moved through nine transactions to KuCoin deposit addresses.
Fake Ledger Live App Raises Questions on Apple App Store Review
The incident draws attention to Apple’s App Store review process. The counterfeit app cleared automated scans and manual checks despite rules that bar impersonation and unauthorized data collection. Apple has issued no public statement on how the clone passed review.
Analyst Shanaka Anslem Perera highlighted the timing and broader context. “On April 3, Apple filed a Supreme Court petition arguing its App Store commission is justified by the security value of its ecosystem,” he wrote. “On April 11, five days later, a fake Ledger Live app sailed through that same ecosystem, past the automated scans, past the manual reviewers.”
KuCoin received many of the stolen funds through its deposit addresses. The exchange continues to face regulatory scrutiny following its EU onboarding ban in February 2026 and previous U.S. penalties of more than $300 million in January 2025.
ChainStreet’s Take
Self-custody users already shoulder the full weight of protecting seed phrases. A convincing fake of one of the best-known wallet brands made it through Apple’s distribution system and stole millions in days.
The rule stays blunt. Never enter recovery words into software downloaded from any app store. Verify the developer account directly and download only from official sources. Any prompt that asks for a seed phrase counts as an immediate red flag.
The $9.5 million taken in one week shows how fast trust in familiar names can turn against users. For the crypto community, vigilance around every installation source stays the only reliable defense.
Activate Intelligence Layer
Institutional-grade structural analysis for this article.






