Security researchers identify a high-risk chain of four vulnerabilities in OpenClaw that exposes roughly 245,000 autonomous AI agent servers to unauthenticated remote code execution. The flaws enable unauthorized parties to seize control of server instances and exfiltrate sensitive data by exploiting the elevated permissions typically granted to autonomous agents.
- OpenClaw maintainers release emergency patches after researchers identify a high-risk chain of four vulnerabilities in the autonomous AI agent framework.
- Shodan and ZoomEye scans confirm 245,000 server instances remain exposed to unauthenticated remote code execution and systemic credential theft.
- Cyera Research warns that the high-level privileges granted to autonomous agents allow attackers to weaponize AI systems for internal network infiltration.
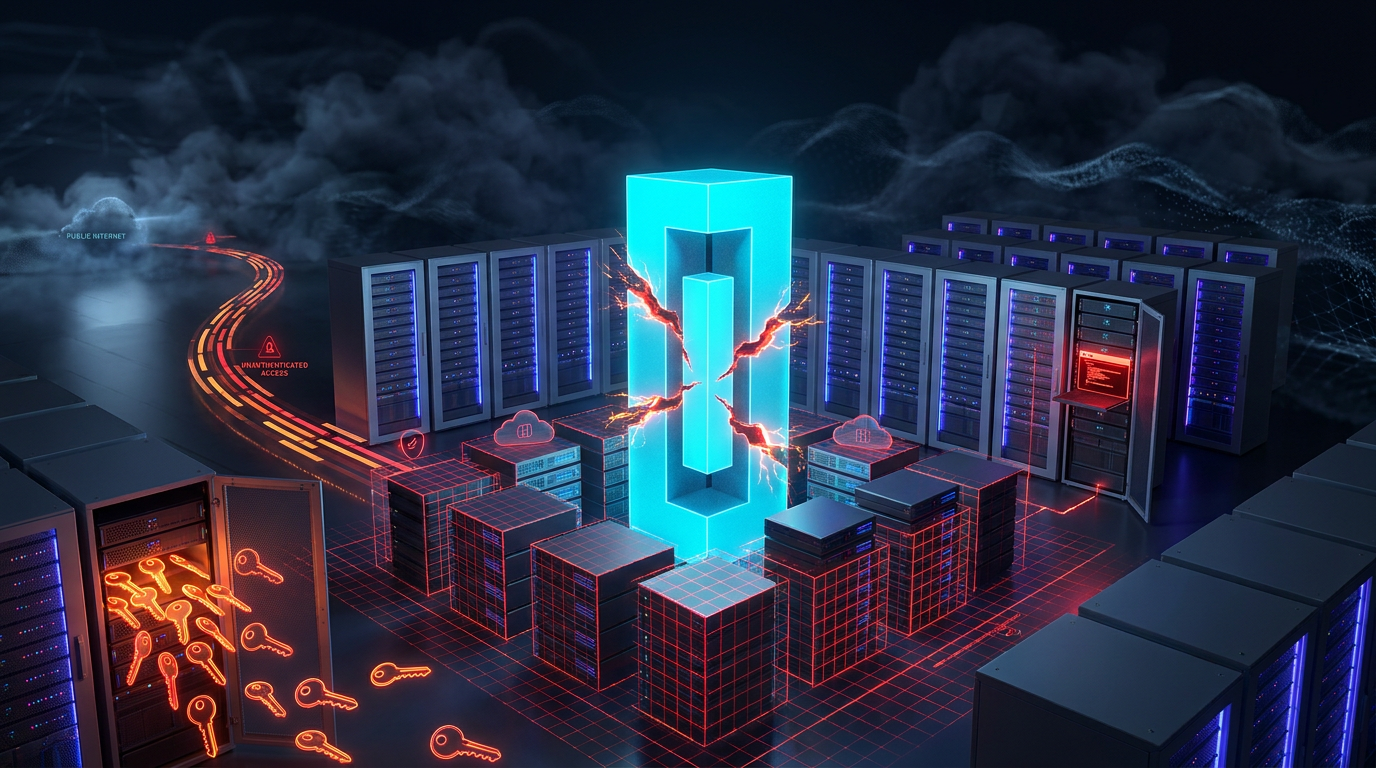
A chain of four critical vulnerabilities in OpenClaw, a framework for building autonomous AI agents, left an estimated 245,000 publicly accessible server instances vulnerable. The security flaws enabled remote code execution and credential theft. Attackers gained the ability to install persistent backdoors by leveraging the inherent privileges of the agent.
Shodan and ZoomEye scans confirmed the scale of the exposure. Shodan identified 65,000 publicly facing OpenClaw instances. ZoomEye recorded approximately 180,000 instances. The vulnerabilities surfaced in early May 2026 and allowed attackers to bypass authentication. A report from Cyera Research revealed that the flaws “allow attackers to bypass authentication and execute arbitrary commands with the privileges of the running AI agent.”
The four vulnerabilities formed a dangerous attack chain. The first flaw allowed unauthenticated access to sensitive endpoints. Subsequent issues enabled privilege escalation and arbitrary code execution within the environment of the agent. OpenClaw agents often ran with high privileges to perform file operations and network requests. A successful exploit gave attackers full control over the compromised server. Security researchers noted that the design of the platform inadvertently created a high-risk environment when deployed publicly without proper hardening.
The exposure concerned industry experts because OpenClaw powered a wide range of experimental and production AI agent deployments. Many instances ran on cloud servers with public IP addresses. Discovering these servers required only basic scanning tools. The ability to weaponize the capabilities of the agent meant attackers used the compromised AI to exfiltrate data and pivot to internal networks. No evidence of widespread exploitation surfaced immediately. Security teams urged immediate patching for all OpenClaw deployments.
Genuine News Deserves Honest Attention.
High-conviction projects require an intelligent audience. Connect with readers who value sharp reporting.
👉 Submit Your PRMaintainers of OpenClaw released emergency patches shortly after the vulnerabilities became public. The project team advised users to update immediately. They also recommended a review of deployment configurations to restrict public access. “The project team noted that the flexibility of the framework was a core feature but acknowledged that it created unforeseen risks in public deployments,” a statement from the maintainers said. The incident highlighted the security challenges of rapidly evolving open-source AI frameworks. Speed of development often outpaced rigorous security auditing in the agent sector.
Chain Street’s Take
The OpenClaw vulnerabilities reveal a fundamental security paradox in the autonomous agent sector. By granting these systems high-level permissions to maximize their utility, developers inadvertently created a roadmap for lateral movement within cloud environments. Security teams face a difficult choice between the operational freedom of an AI agent and the rigid network isolation required to prevent a repeat of such large-scale exposures. The rapid adoption of open-source frameworks without hardened defaults suggests that the industry prioritized functionality over the structural safety required for production-grade deployments.
Activate Intelligence Layer
Institutional-grade structural analysis for this article.